Professor of Applied Informatics
Democritus University of Thrace, Department of Civil Engineering, in the School of Engineering, Xanthi, Greece

Professor of Applied Informatics, Democritus University of Thrace, School of Engineering, Department of Civil Engineering, Faculty of Mathematics, Programming and general courses, Lab of Mathematics and Informatics (ISCE)
Democritus University of Thrace, Department of Civil Engineering, in the School of Engineering, Xanthi, Greece
Greek Open University, School of Positive Sciences and Informatics, Greece
Democritus University of Thrace, Department of Forestry and Management of the Environment and Natural Resources, School of Agricutlure and Forest Sciences, Orestiada, Greece
University of Western Makedonia, Department of Information and Communication Engineering, Kozani, Greece
University of Makedonia, Department of Applied Informatics, Thessaloniki, Greece
Doctor of Philosophy in the topic of Expert Systems
Aristotle University of Thessaloniki, Lab of Forest Informatics, Greece
Master in Computer Science
Department of Computer Science and Mathematics, University of Wales, University College of Swansea, Great Britain
Bachelor of Science in Mathematics
Department of Mathematics from the School of Positive Sciences, Aristotle University of Thessaloniki, Greece
My research interests cover several aspects of Computational Intelligence, Expert Systems, Multiagent Systems, Fuzzy Theory, Clustering, and Support Vector Machines, focusing mainly on applications in Decision Support Systems, Pattern Recognition, Neural Networks, Machine Learning, Intelligent Optimization and real-world problem solving.
Information and details about the research projects of my research team can be found in this section.
This page contains various information for current members of my Research Team. All personnel are responsible for reviewing and applying the information in the research projects, its applicable plans, and all University, school, departmental and laboratory policies and procedures.
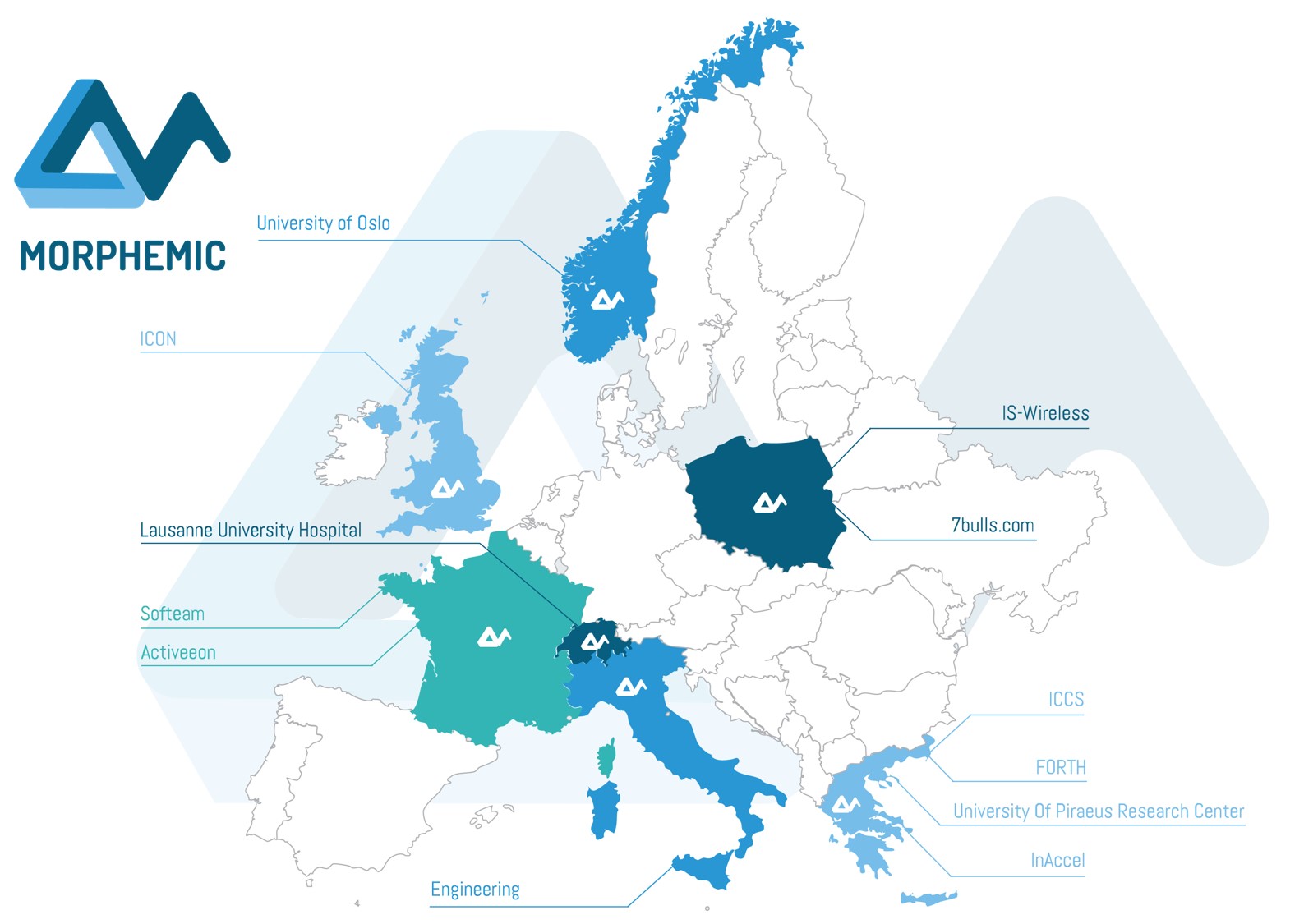
Participation in the Horizon Research Project MORPHEMIC (“Modelling and Orchestrating heterogeneous Resources and Polymorphic applications for Holistic Execution and adaptation of Models in the Cloud”) which is run by the University of Piraeus (April 2021-31/12/2022), Horizon Research Project MORPHEMIC

Research Project entitled, “Cybersecurity Algorithms for Spiking Neural Networks”. BrainChip, Inc., Aliso Viejo, California, U.S.A and School of Civil Engineering, Democritus University of Thrace, Greece, BrainChip Acquires License to Cybersecurity Technology

European Research Council – National Strategic Reference Framework – ΚΕ 2140 Distributed System of Intelligent Agents for the monitoring and facing serious changes in the levels of air pollution and Heat Index in real time (AID) (Air pollution Intelligent Defense), read more

European Research Council – National Strategic Reference Framework – Cooperation 2011 Real Time Operational Control Tool of Combined Sewerage Overflows (SCO) at Coastal Cities, read more
My research is focused, but not limited to, on artificial neural networks, fuzzy logic, decision support systems, multiagent systems and machine learning.
My Google Scholar profile, link
My DBLP Computer Science Bibliography profile, link
Complete list of Publications, link
Below are some of the most recent publications on my research areas.
It is a fact that natural disasters often cause severe damage both to ecosystems and humans. Moreover, man-made disasters can have enormous moral and economic consequences for people. A typical example is the large deadly and catastrophic explosion in Beirut on 4 August 2020, which destroyed a very large area of the city. This research paper introduces a Geo-AI disaster response computer vision system, capable to map an area using material from Synthetic Aperture Radar (SAR). SAR is a unique form of radar that can penetrate the clouds and collect data day and night under any weather conditions. Specifically, the Memory-Augmented Deep Convolutional Echo State Network (MA/DCESN) is introduced for the first time in the literature, as an advanced Machine Vision (MAV) architecture. It uses a meta-learning technique, which is based on a memory-augmented approach. The target is the employment of Deep Reservoir Computing (DRC) for domain adaptation. The developed Deep Convolutional Echo State Network (DCESN) combines a classic Convolutional Neural Network (CNN), with a Deep Echo State Network (DESN), and analog neurons with sparse random connections. Its training is performed following the Recursive Least Square (RLS) method. In addition, the integration of external memory allows the storage of useful data from past processes, while facilitating the rapid integration of new information, without the need for retraining. The proposed DCESN implements a set of original modifications regarding training setting, memory retrieval mechanisms, addressing techniques, and ways of assigning attention weights to memory vectors. As it is experimentally shown, the whole approach produces remarkable stability, high generalization efficiency and significant classification accuracy, significantly extending the state-of-the-art Machine Vision methods, pdf
Attackers are perpetually modifying their tactics to avoid detection and frequently leverage legitimate credentials with trusted tools already deployed in a network environment, making it difficult for organizations to proactively identify critical security risks. Network traffic analysis products have emerged in response to attackers’ relentless innovation, offering organizations a realistic path forward for combatting creative attackers. Additionally, thanks to the widespread adoption of cloud computing, Device Operators (DevOps) processes, and the Internet of Things (IoT), maintaining effective network visibility has become a highly complex and overwhelming process. What makes network traffic analysis technology particularly meaningful is its ability to combine its core capabilities to deliver malicious intent detection. In this paper, we propose a novel darknet traffic analysis and network management framework to real-time automating the malicious intent detection process, using a weight agnostic neural networks architecture. It is an effective and accurate computational intelligent forensics tool for network traffic analysis, the demystification of malware traffic, and encrypted traffic identification in real time. Based on a weight agnostic neural networks (WANNs) methodology, we propose an automated searching neural net architecture strategy that can perform various tasks such as identifying zero-day attacks. By automating the malicious intent detection process from the darknet, the advanced proposed solution is reducing the skills and effort barrier that prevents many organizations from effectively protecting their most critical assets, pdf
With the advent of the first pandemic wave of Severe Acute Respiratory Syndrome Coronavirus-2 (SARS-CoV-2), the question arises as to whether the spread of the virus will be controlled by the application of preventive measures or will follow a different course, regardless of the pattern of spread already recorded. These conditions caused by the unprecedented pandemic have highlighted the importance of reliable data from official sources, their complete recording and analysis, and accurate investigation of epidemiological indicators in almost real time. There is an ongoing research demand for reliable and effective modeling of the disease but also the formulation of substantiated views to make optimal decisions for the design of preventive or repressive measures by those responsible for the implementation of policy in favor of the protection of public health. The main objective of the study is to present an innovative data-analysis system of COVID-19 disease progression in Greece and her border countries by real-time statistics about the epidemiological indicators. This system utilizes visualized data produced by an automated information system developed during the study, which is based on the analysis of large pandemic-related datasets, making extensive use of advanced machine learning methods. Finally, the aim is to support with up-to-date technological means optimal decisions in almost real time as well as the development of medium-term forecast of disease progression, thus assisting the competent bodies in taking appropriate measures for the effective management of the available health resources, pdf
The complexity of threats in the ever-changing environment of modern industry is constantly increasing. At the same time, traditional security systems fail to detect serious threats of increasing depth and duration. Therefore, alternative, intelligent solutions should be used to detect anomalies in the operating parameters of the infrastructures concerned, while ensuring the anonymity and confidentiality of industrial information. Blockchain is an encrypted, distributed archiving system designed to allow for the creation of real-time log files that are unequivocally linked. This ensures the security and transparency of transactions. This research presents, for the first time in the literature, an innovative Blockchain Security Architecture that aims to ensure network communication between traded Industrial Internet of Things devices, following the Industry 4.0 standard and based on Deep Learning Smart Contracts. The proposed smart contracts are implementing (via computer programming) a bilateral traffic control agreement to detect anomalies based on a trained Deep Autoencoder Neural Network. This architecture enables the creation of a secure distributed platform that can control and complete associated transactions in critical infrastructure networks, without the intervention of a single central authority. It is a novel approach that fuses artificial intelligence in the Blockchain, not as a supportive framework that enhances the capabilities of the network, but as an active structural element, indispensable and necessary for its completion, pdf
The backbone of the economy, security and sustainability of a state is inseparably linked to the security of its critical infrastructure. Critical infrastructures define goods, systems or subsystems that are essential to maintain the vital functions of society, health, physical protection, security plus economic and social well-being of citizens. The digital security of critical infrastructures is a very important priority for the well-being of every country, especially nowadays, because of the direct threats dictated by the current international conjuncture and due to the emerging interactions or interconnections developed between the National Critical Infrastructures, internationally. The aim of this research is the development and testing of an Anomaly Detection intelligent algorithm that has the advantage to run very fast with a small portion of the available data and to perform equally well with the existing approaches. Such a system must be characterized by high efficiency and very fast execution. Thus, we present the Gryphon advanced intelligence system. Gryphon is a Semi-Supervised Unary Anomaly Detection System for big industrial data which is employing an evolving Spiking Neural Network (eSNN) One-Class Classifier (eSNN-OCC). This machine learning algorithm corresponds to a model capable of detecting very fast and efficiently, divergent behaviors and abnormalities associated with cyberattacks, which are known as Advanced Persistent Threat (APT). The training process is performed on data related to the normal function of a critical infrastructure, pdf
According to the latest projections of the International Energy Agency, smart grid technologies have become essential to handling the radical changes expected in international energy portfolios through 2030. A smart grid is an energy transmission and distribution network enhanced through digital control, monitoring, and telecommunication capabilities. It provides a real-time, two-way flow of energy and information to all stakeholders in the electricity chain, from the generation plant to the commercial, industrial, and residential end user. New digital equipment and devices can be strategically deployed to complement existing equipment. Using a combination of centralized IT and distributed intelligence within critical system control nodes ranging from thermal and renewable plant controls to grid and distribution utility servers to cities, commercial and industrial infrastructures, and homes a smart grid can bring unprecedented efficiency and stability to the energy system. Information and communication infrastructures will play an important role in connecting and optimizing the available grid layers. Grid operation depends on control systems called Supervisory Control and Data Acquisition (SCADA) that monitor and control the physical infrastructure. At the heart of these SCADA systems are specialized computers known as Programmable Logic Controllers (PLCs). There are destructive cyber-attacks against SCADA systems as Advanced Persistent Threats (APT) were able to take over the PLCs controlling the centrifuges, reprogramming them in order to speed up the centrifuges, leading to the destruction of many and yet displaying a normal operating speed in order to trick the centrifuge operators and finally can not only shut things down but can alter their function and permanently damage industrial equipment. This paper proposes a computational intelligence System for Identification Cyber-Attacks on the Smart Energy Grids (SICASEG). It is a big data forensics tool which can capture, record, and analyze the smart energy grid network events to find the source of an attack to both prevent future attacks and perhaps for prosecution, pdf
It is a fact that more and more users are adopting the online digital payment systems via mobile devices for everyday use. This attracts powerful gangs of cybercriminals, which use sophisticated and highly intelligent types of malware in order to broaden their attacks. Malicious software is designed to run quietly and to remain unsolved for a long time. It manages to take full control of the device and to communicate (via the Tor network) with its Command & Control (C & C) servers of fast-flux botnets’ networks to which it belongs. This is done in order to achieve the malicious objectives of the botmasters. This paper proposes the development of the Computational Intelligence Anti-Malware Framework (CIantiMF) which is innovative, ultra-fast and it has low requirements. It runs under the Android Operating System (OS) and its reasoning is based on advanced Computational Intelligence approaches. The selection of the Android OS was based on its popularity and on the number of critical applications available for it. The CIantiMF uses two advanced technology extensions for the ART JVM (Java Virtual Machine) which is the default in the recent versions of Android. The first is the Smart Anti-Malware Extension (SAME), which can recognize whether the Java classes of an Android application are benign or malicious by using an optimized Multi-Layer Perceptron (MLP). The optimization is done by the employment of the Biogeography-Based Optimizer algorithm (BBO). The second is the Tor Online Traffic Identification Extension (OTTIE), which is capable of achieving malware localization, Tor traffic identification and botnets prohibition, with the use of the Online Sequential Extreme Learning Machine (OSELM) algorithm.
Θεωρία και υλοποίηση ευφυών συστημάτων σε περιβάλλον MATLAB, WEKA, NEURALWORKS II PLUS, eSNN-IPython, JADE, CLIPS, LEONARDO.
Περί Ευφυΐας, Ασαφής Λογική, Ευφυή Συστήματα Ασαφούς Λογικής, Συστήματα Κανόνων-Έμπειρα Συστήματα, Έμπειρα Συστήματα Ασαφούς Λογικής, Μεθοδολογίες Αξιολόγησης Έμπειρων Συστημάτων, Κελύφη-Περιβάλλοντα Ανάπτυξης Έμπειρων Συστημάτων LEONARDO-CLIPS, Τεχνητά Νευρωνικά Δίκτυα, Ανάπτυξη Τεχνητών Νευρωνικών Δικτύων στο Περιβάλλον MATLAB, Μη Κατευθυνόμενη Μηχανική Μάθηση, Πολυπρακτορικά Συστήματα Το Σύστημα Ευφυών Πρακτόρων AID, Μηχανές Διανυσμάτων Υποστήριξης (SUPPORTVECRORMACHINES), Δεδομένα-Ασκήσεις, Βιβλιογραφία, Ευρετήριο.
The need to protect the environment, biodiversity and to safeguard public health requires the development of timely and reliable methods for the identification of particularly dangerous invasive species, before they become regulators of ecosystems. These species appear morphologically similar, despite their strong biological differences, something that complicates their identification process. Additionally, the localization of the broader space of dispersion and development of invasive species is considered of critical importance, in an effort to take the proper management measures. The aim of this research is to create an advanced computational intelligence system for the automatic recognition, of invasive or other unknown species. The identification is performed based on the analysis of environmental DNA (eDNA) by employing machine learning methods. More specifically, this research effort proposes a hybrid bio-inspired computational intelligence detection approach. It employs Extreme Learning Machines combined with an evolving Izhikevich spiking neuron model, for the automated identification of the extremely dangerous for human health invasive fish species “Lagocephalus Sceleratus”.

Soft Computing Modeling of Wild Fire Risk Indices: The Risk Profile of Peloponnesus Region in Greece
It is essential to find ways that can reduce the risk of devastating forest fires which have multiple negative ecological and financial consequences. This preliminary research effort focuses on the implementation of an intelligent rule based fuzzy inference system evaluating wild fire risk in the forest departments of Greece. The system uses soft computing techniques and was built in the Matlab integrated environment. The whole research is related to the wild fires in Greece during the period 1983-1997 with data coming from the general forest management service. It classifies all Greek forest departments (by assigning three labels) according to their forest fire risk due to distinct parameters. The estimation of the risk indices was done by using fuzzy triangular membership functions and Einstein fuzzy conjunction T-Norms. Moreover the system produces the profile of the forest departments located in the geographic area of “Peloponnesus.” This is a region located in the southern part of the country and it has a vast number of annual forest fire breakouts. Meteorological, topographic, and historical (total burned area and intervention time) features were considered for the determination of the risk indices. The system has shown a good performance which can be improved further if more data is gathered and used. Its main advantage is that it offers an innovative and reliable model that can be employed in any part of the world as a basis for natural disasters’ risk estimation.
Developing neural networks to investigate relationships between air quality and quality of life indicators
Quality of life (QOL) is an integral outcome measure in the management of diseases. It can be used to assess the results of different management methods, in relation to disease complications and in fine-tuning management methods (Koller & Lorenz, 2003). Quantitative analysis of quality of life across countries, and the construction of summary indices for such analyses have been of interest for some time (Slottje et al., 1991). Most early work focused on largely single dimensional analysis based on such indicators as per capita GDP, the literacy rate, and mortality rates. Maasoumi (1998) and others called for a multidimensional quantitative study of welfare and quality of life. The argument is that welfare is made up of several distinct dimensions, which cannot all be monetized, and heterogeneity complications are best accommodated in multidimensional analysis. Hirschberg et al. (1991) and Hirschberg et al. (1998) identified similar indicators, and collected them into distinct clusters which could represent the dimensions worthy of distinct treatment in multidimensional frameworks. In this research effort we have considered the role of air quality indicators in the context of economic and welfare life quality indicators, using artificial neural networks (ANN). Therefore in this presentation we have obtained the key variables (life expectancy, healthy life years, infant mortality, Gross Domestic Product (GDP) and GDP growth rate) and developed a neural network model to predict the air quality outcomes (emissions of sulphur and nitrogen oxides). Sustainability and quality of life indicators have been proposed recently by Flynn et al. (2002) and life quality indices have been used to estimate willingness to pay (Pandey & Nathwani, 2004). The innovative part of this research effort lies in the use of a soft computing machine learning approach like the ANN to predict air quality. In this way, we introduce the reader to a technique that allows the comparison of various attributes that impact the quality of life in a meaningful way.
Air pollution is the problem of adding harmful substances or other agents into the atmosphere and it is caused by industrial, transport or household activities. It is one of the most serious problems of our times and the determination of the conditions under which we have extreme pollutants' values is a crucial challenge for the modern scientific community. The innovative and effective hybrid algorithm designed and employed in this research effort is entitled Easy Hybrid Forecasting (EHF). The main advantage of the EHF is that each forecasting does not require measurements from sensors, other hardware devices or data that require the use of expensive software. This was done intentionally because the motivation for this work was the development of a hybrid application that can be downloaded for free and used easily by everyday common people with no additional financial cost, running in devices like smart phones. From this point of view it does not require data from sensors or specialized software and it can offer people reliable information about extreme cases.
AOne of the direct consequences of climate change lies in the spread of invasive species, which constitute a serious and rapidly worsening threat to ecology, preservation of natural biodiversity and protection of flora and fauna. It can even be a potential threat to the health of humans. These species, do not appear to have serious morphological variations, despite their strong biological differences. Due to this fact their identification process is often quite difficult. The need to protect the environment and safeguard public health, requires the development of advanced methods for early and accurate identification of some particularly dangerous invasive species, in order to plan and apply specific and effective management measures. The aim of this study is to create an advanced computer vision system for the automatic recognition of invasive or other unknown species, based on their phenotypes. More specifically, this research proposes an innovative and very effective Extreme Learning Machine (ELM) model, which is optimized by the Adaptive Elitist Differential Evolution algorithm (AEDE). The AEDE is an improved version of the differential evolution (DE) algorithm and it is proper for big data resolution. Feature selection is done by using deep learning Convolutional Neural Networks. A Geo Location system is used to detect the invasive species by Comparing with the local species of the region under research.

Είναι γεγονός ότι στις ημέρες μας πολύ συχνά προκύπτει η αναγκαιότητα άμεσης εκτίμησης δεικτών επικινδυνότητας (με τη μορφή αδιάστατων αριθμών) μέσα σε ένα ασαφές πολύπλοκο περιβάλλον και με περιορισμένο όγκο διαθέσιμων δεδομένων. Όπως φαίνεται και στο τελευταίο κεφάλαιο που περιγράφει την περίπτωση των αυτόνομων πρακτόρων που έχουν τη δυνατότητα αυτοοργάνωσης, ένα σύστημα μπορεί να συμπεριφέρεται χαοτικά, ακόμα και όταν είναι γνωστές οι αρχικές του συνθήκες, αλλά και οι κανόνες λειτουργίας του!! Χρειαζόμαστε λοιπόν ευέλικτα πρότυπα, ικανά να ανταποκριθούν στις ανάγκες μας για την εξομοίωση πραγματικών καταστάσεων. Σε αυτόν τον τόμο λοιπόν παρατίθενται αρκετές διαφορετικές προσεγγίσεις σχεδίασης, ανάπτυξης και αξιολόγησης ευφυών πληροφοριακών συστημάτων, όπως τα έμπειρα συστήματα και ο χειρισμός της αβεβαιότητας-ασάφειας, τα συστήματα ασαφούς άλγεβρας και λογικής και ειδικότερα τα συστήματα που παίρνουν αποφάσεις, ακόμα και με λίγα ή ελλιπή δεδομένα. Επίσης παρουσιάζονται βασικές αρχές από τα τεχνητά νευρωνικά δίκτυα και ειδικότερα τα δίκτυα ασυνεχούς εκπομπής και εξομοίωσης βιολογικών αντίστοιχων, αλλά και τα συστήματα αυτόνομων πρακτόρων. Σε κάθε προσέγγιση γίνεται παρουσίαση μιας εφαρμογής εκτίμησης της επικινδυνότητας, σε διάφορα προβλήματα φυσικών καταστροφών. Η αξιολόγηση αυτή γίνεται κάτω από διαφορετικές οπτικές γωνίες, έτσι ώστε αυτή να είναι σφαιρική και να καλύπτει, όσο είναι αυτό δυνατόν, όλα τα ενδεχόμενα. Πρόκειται για σύγχρονα ευέλικτα υπολογιστικά συστήματα που έχουν τη δυνατότητα να υλοποιούν σενάρια, ακόμα και με τους πιο απρόβλεπτους παράγοντες και να συλλαμβάνουν και να αξιοποιούν σε ικανοποιητικό βαθμό έννοιες του πραγματικού κόσμου που έχουν ποιοτικό χαρακτήρα και είναι αδύνατον να αποδοθούν με τα κλασικά μαθηματικά.
Several machine learning models were used to predict interior spruce wood density using data from open-pollinated progeny testing trial. The data set consists of growth (height and diameter which were used to estimate individual tree volume) and wood quality (wood density determined by X-ray densitometry, resistance to drilling, and acoustic velocity) attributes for a total of 1,146 trees growing on comparable sites in interior British Columbia. Various machine learning models were developed for estimating wood density. The Multi Layer Feed Forward (MLFF) artificial neural networks and Gene Expression Programming (GEP) provided the highest predictability as compared to the other methods tested, including those based on classical multiple regression which was considered as the comparisons benchmark. The utilization of machine learning models as a credible method for estimating wood density using available growth data as an indirect method for determining trees wood density is expected to become increasingly helpful to forest managers and tree breeders.
The analysis of air quality and the continuous monitoring of air pollution levels are important subjects of the environmental science and research. This problem actually has real impact in the human health and quality of life. The determination of the conditions which favor high concentration of pollutants and most of all the timely forecast of such cases is really crucial, as it facilitates the imposition of specific protection and prevention actions by civil protection. This research paper discusses an innovative three folded intelligent hybrid system of combined machine learning algorithms HISYCOL (henceforth). First it deals with the correlation of the conditions under which high pollutants concentrations emerge. On the other hand it proposes and presents an ensemble system using combination of machine learning algorithms capable of forecasting the values of air pollutants (VAP). What is really important and gives this modeling effort a hybrid nature is the fact that it uses clustered datasets. Moreover this approach improves the accuracy of existing forecasting models by using unsupervised machine learning to cluster the data vectors and trace hidden knowledge. Finally it employs a Mamdani fuzzy inference system for each air pollutant in order to forecast even more effectively its concentrations.
Air pollution is directly linked with the development of technology and science, the progress of which besides significant benefits to mankind it also has adverse effects on the environment and hence on human health. The problem has begun to take worrying proportions especially in large urban centers, where 60,000 deaths are reported each year in Europe's towns and 3,000,000 worldwide, due to long-term air pollution exposure (exposure of the European Agency for the Environment http://www.eea.europa.eu/). In this paper we propose a novel and flexible hybrid machine learning system that combines Semi-Supervised Classification and Semi-Supervised Clustering, in order to realize prediction of air pollutants outliers and to study the conditions that favor their high concentration.
Air pollution is related to the concentration of harmful substances in the lower layers of the atmosphere and it is one of the most serious problems threatening the modern way of life. Determination of the conditions that cause maximization of the problem and assessment of the catalytic effect of relative humidity and temperature are important research subjects in the evaluation of environmental risk. This research effort describes an innovative model towards the forecasting of both primary and secondary air pollutants in the center of Athens, by employing Soft Computing Techniques. More specifically, Fuzzy Cognitive Maps are used to analyze the conditions and to correlate the factors contributing to air pollution. According to the climate change scenarios till 2100, there is going to be a serious fluctuation of the average temperature and rainfall in a global scale. This modeling effort aims in forecasting the evolution of the air pollutants concentrations in Athens as a consequence of the upcoming climate change.
Climate change combined with the increase of extreme weather phenomena, has significantly influenced marine ecosystems, resulting in water overheating, increase of sea level and rising of the acidity of surface waters. The potential impacts in the biodiversity of sensitive ecosystems (such as Mediterranean sea) are obvious. Many organisms are under extinction, whereas other dangerous invasive species are multiplied and thus they are destroying the ecological equilibrium. This research paper presents the development of a sophisticated, fast and accurate Food Pathogen Detection (FPD) system, which uses the biologically inspired Artificial Intelligence algorithm of Extreme Learning Machines. The aim is the automated identification and control of the extremely dangerous for human health invasive fish species “Lagocephalus Sceleratus”. The matching is achieved through extensive comparisons of protein and DNA sequences, known also as DNA barcodes following an ensemble learning approach.
It is well known that cyber criminal gangs are already using advanced and especially intelligent types of Android malware, in order to overcome the out-of-band security measures. This is done in order to broaden and enhance their attacks which mainly target financial and credit foundations and their transactions. It is a fact that most applications used under the Android system are written in Java. The research described herein, proposes the development of an innovative active security system that goes beyond the limits of the existing ones. The developed system acts as an extension on the ART (Android Run Time) Virtual Machine architecture, used by the Android Lolipop 5.0 version. Its main task is the analysis and classification of the Java classes of each application. It is a flexible intelligent system with low requirements in computational resources, named Smart Anti Malware Extension (SAME). It uses the biologically inspired Biogeography-Based Optimizer (BBO) heuristic algorithm for the training of a Multi-Layer Perceptron (MLP) in order to classify the Java classes of an application as benign or malicious. SAME was run in parallel with the Particle Swarm Optimization (PSO), Ant Colony Optimization (ACO) and Genetic Algorithm (GA) and it has shown its validity.
Domain Generation Algorithm (DGA) has evolved as one of the most dangerous and “undetectable” digital security deception methods. The complexity of this approach (combined with the intricate function of the fast-flux “botnet” networks) is the cause of an extremely risky threat which is hard to trace. In most of the cases it should be faced as a zero-day vulnerability. This kind of combined attacks is responsible for malware distribution and for the infection of Information Systems. Moreover it is related to illegal actions, like money mule recruitment sites, phishing websites, illicit online pharmacies, extreme or illegal adult content sites, malicious browser exploit sites and web traps for distributing virus. Traditional digital security mechanisms phase such vulnerabilities in a conventional manner, they create often false alarms and they fail to forecast them. This paper proposes an innovative fast and accurate evolving Smart URL Filter (eSURLF) in a Zone-based Policy Firewall (ZFW) which uses evolving Spiking Neural Networks (eSNN) for detecting algorithmically generated malicious domains names.
Confidentiality, Integrity and Availability of Military information is a crucial and critical factor for a country’s national security. The security of military Information Systems (MIS) and Networks (MNET) is a subject of continuous research and design, due to the fact that they manage, store, manipulate and distribute the information. This study presents a Bio-Inspired Hybrid Artificial Intelligence Framework for Cyber Security (bioHAIFCS). This framework combines timely and bio inspired Machine Learning methods suitable for the protection of critical network applications namely military information systems, applications and networks. More specifically, it combines a) the Hybrid Evolving Spiking Anomaly Detection Model (HESADM), which is used in order to prevent in time and accurately, cyber-attacks, which cannot be avoided by using passive security measures namely: Firewalls, b) the Evolving Computational Intelligence System for Malware Detection (ECISMD) that spots and isolates malwares located in packed executables untraceable by antivirus c) the Evolutionary Prevention System from SQL Injection (ePSSQLI) attacks, which early and smartly forecasts the attacks using SQL Injections methods.
According to the Greek mythology, Ladon was the huge dragon with the 100 heads, which had the ability to stay continuously up, in order to guard the golden “Esperides” apples in the tree of life. Alike the ancient one, digital Ladon is an advanced information systems’ security mechanism, which uses Artificial Intelligence to protect, control and offer early warning in cases of detour or misleading of the digital security measures. It is an effective cross-layer system of network supervision, which enriches the lower layers of the system (Transport, Network and Data). It amplifies in an intelligent manner the upper layers (Session, Presentation and Application) with capabilities of automated control. This is done to enhance the energetic security and the mechanisms of reaction of the general system, without special requirements in computational resources. This paper describes the development of Ladon which is an advanced, incredibly fast and low requirements’ effective filter, that performs analysis of network flow. Ladon uses Online Sequential Extreme Learning Machine with Gaussian Radial Basis Function kernel in order to perform network traffic classification, malware traffic analysis and fast-flux botnets localization.